IT responds to phishing scams
January 26, 2024
Editor’s Note, Friday, February 2, at 11:09 a.m.: A previous version of this article mistakenly reported that 709,650 phishing emails were received by the College from January 14-20. This article has been updated to reflect that the college received 709,650 emails.
The coastal town of Brunswick has recently reeled in a different kind of “phish”—a number of email scams targeting Bowdoin students. Over the break, many Bowdoin students have been targeted by a wave of online email scams meant to obtain students’ personal information.
An email phishing scam is a type of internet scam in which online miscreants—known as “threat actors”—attempt to obtain sensitive information from users, such as their username or password. More malicious phishing attempts seek victims’ addresses, credit card information or social security numbers. Oftentimes, threat actors will attempt to access this information by getting victims to click on links in the body of the email.
At the end of the fall semester and into Winter Break, there were three large-scale attacks on students’ emails. Information Technology (IT)’s Senior Director and Chief Information Security Officer Jeff Doring said that a wave of attacks like this is not abnormal during finals and break time.
Doring said that threat actors will often target students during this hectic time of the school year when students’ guard is down. The recent flood of scams included a fake Covid-19 tracker and solicitation of credential information, among other tactics.
“Phishing is part of life. [It’s] going to happen. We get them all the time,” Doring said. “Students are taking exams, packing up and saying goodbye. That’s an opportune phish.”
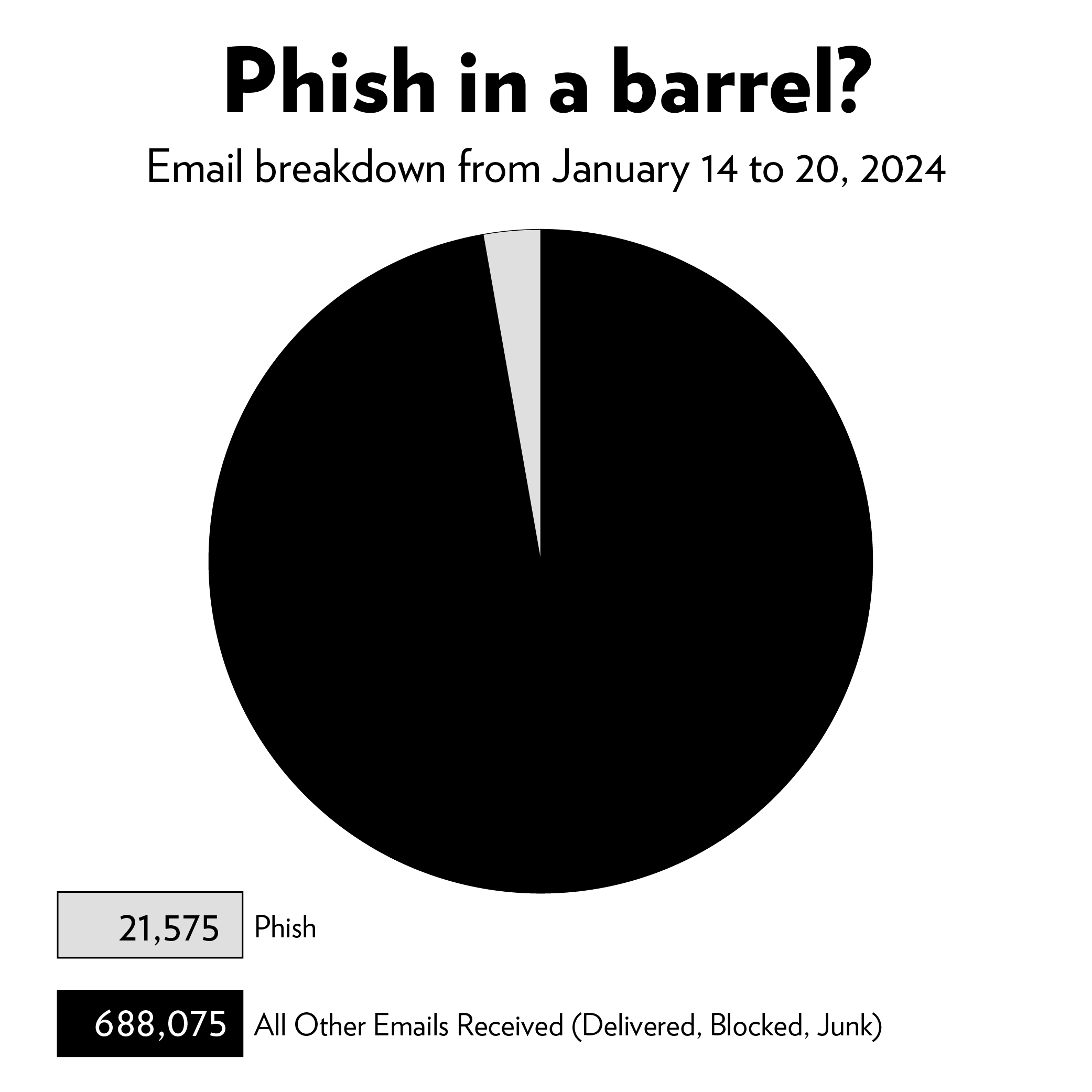
According to data provided to the Orient by Doring, during the week of January 14, the College’s email accounts received a total of 709,650 emails. Of those, 21,757 emails—or three percent—were automatically identified by the IT department’s security system as phishing emails and blocked.
 Shihab Moral
Shihab MoralIn response to the recent surge of phishing attacks, Doring said that the College is remaining vigilant. The largest change coming for students’ online security is a complete move to Okta for login verification. Once this step is complete, Doring said that the College will move to a passwordless system. Additionally, he hopes to work with administration to make cyber awareness training part of first-year orientation.
Doring stressed that student awareness is the most important defense against phishing. He advises students to use password management software and to have passwords with at least 12 characters.
Further, he advises students to look at the sender’s address and never click on suspicious links.
“It’s important to understand that reaching zero phishing emails is not the goal. Community education combined with a balanced algorithm is the optimal end game,” Doring wrote in an email to the Orient.
Other Maine colleges, however, do not have as many problems with phishing scams. Bates College has managed to avoid many large-scale attacks. Chad Tracy, Bates’ director of information security, privacy and compliance attributes this to the fact that Bates does not disclose its students’ emails in their directory.
Tracy said that threat actors often look at college directories to build a roster of potential victims.
“These [threat actors] aren’t stupid. This is their business—this is their lifeblood,” Tracy said. “Here at Bates, we thought ‘Let’s take that away.’ If you want to see a student’s email address, you’ll have to [multi-factor] authenticate.”
The Bowdoin Directory optionally allows students to hide their email addresses from campus.
Among the Bowdoin students who were targeted by these would-be scammers was Everett Gordon ’26, who was sent an email from someone claiming to be President Safa Zaki. The email requested Gordon’s cell phone number in order to “complete an assignment.” Gordon said the first suspicious part of the email was the sender’s address: fjoeoffice5377@gmail.com.
“It was a very low-level phish, it was pretty funny,” Gordon said. “It caught me off guard … [students] definitely need to be cautious in general about phishing.”
While the phishing attack Gordon encountered was easy to detect, other students were not as lucky. Last year, Hanna Cha ’25 was targeted in a phishing scam that claimed to provide students a job. Cha gave the scammers her personal email and address before she realized she was being attacked.
“As soon as I sent it, I thought, ‘Oh shoot, that was probably stupid,’” Cha said. “I felt embarrassed, but I can make fun of myself at least.”
The threat actor took no further action against Cha.
Although not a victim of the scamming herself, Clara Tunny ’25 is frustrated and hopes the rampant email scams will end soon.
“College students are really vulnerable. You’re broke, busy all the time, and trying to figure out your life. We don’t know about these things,” Tunny said.

Comments
Before submitting a comment, please review our comment policy. Some key points from the policy: